LoadConnect AI browser extension: redefining security in modern logistics software

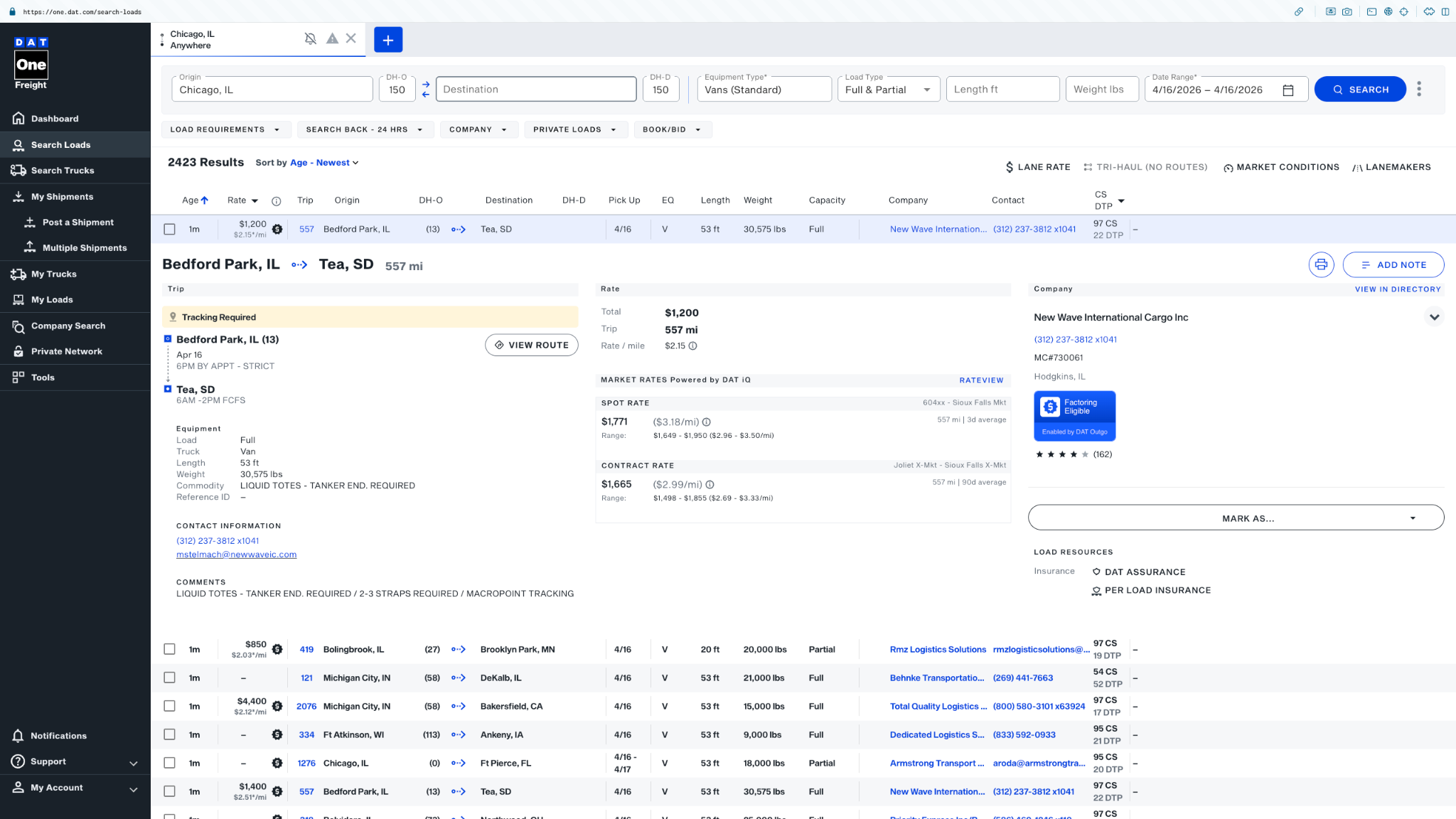
Modern logistics has become fully digital. What used to be phone calls, spreadsheets, and manual coordination is now managed through cloud platforms and specialized tools that power the entire flow of freight operations. Today, most dispatch teams work directly inside browser-based environments, relying on load boards, rate tools, carrier databases, and financial platforms to keep operations moving.
As a result, modern trucking dispatch software is no longer just a back-office system - it has become the central workspace for daily decision-making. Dispatchers now operate across multiple tabs, switching between brokers, loads, pricing tools, and communication systems in real time.
At the same time, the industry is rapidly adopting automation technologies. Companies are integrating dispatch automation solutions to reduce manual workload, speed up decision-making, and improve operational efficiency. Alongside this shift, we are also seeing a growing adoption of AI dispatch software and browser-based tools designed to assist with load selection, rate evaluation, and repetitive dispatch tasks.
One of the most visible trends in this transformation is the rise of the AI browser extension - tools that integrate directly into the dispatcher’s workflow inside the browser and interact with load boards and logistics platforms in real time.
But as the ecosystem becomes more connected and more automated, a less visible question starts to emerge: what exactly are these tools capable of accessing once they are installed?
In a fully browser-based environment, tools do not operate in isolation. They run inside the same space where sensitive operational data is being viewed, processed, and acted upon. This creates a situation where functionality and access are tightly intertwined - and not always clearly understood by users at the moment of installation.
The core issue is not the lack of tools in modern logistics.
It is the lack of clarity about what those tools are actually capable of accessing behind the interface.
The Invisible Risk: How Browser Extensions Actually Work
Browser extensions have become a standard part of modern logistics workflows, especially in environments powered by dispatch software for trucking companies. They are often positioned as simple productivity tools - lightweight assistants that improve how dispatchers interact with load boards and carrier platforms.
However, what is not always obvious to users is how these tools actually function inside the browser environment.
Unlike standalone software, browser extensions do not run in isolation. They operate directly inside the same browser context where operational logistics work is being performed. This means they exist alongside active sessions, open tabs, and authenticated platforms used in daily dispatch operations.
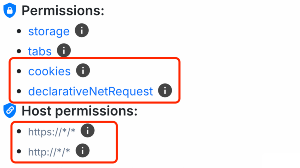
When a browser extension is installed, it requests a set of permissions. These permissions define what the extension is technically allowed to access or interact with. In practice, this means the user is granting a predefined level of access before the tool is even used.
The key challenge is that these permissions are not always intuitive. They often appear as technical or generic statements, while the actual implications of those permissions are not immediately visible in day-to-day usage.
This creates a gap between perception and reality: a tool may look like a simple assistant for dispatch automation, but its permission scope may extend significantly beyond the visible features in its interface.
In practical terms, browser extensions used in AI dispatch software environments can potentially interact with several sensitive layers inside the browser, depending on the permissions granted at installation.
This may include access to:
- Active session states (logged-in environments across logistics platforms)
- Data displayed on load boards and brokerage platforms
- User interactions inside the browser (clicks, inputs, navigation patterns)
- Network-level communication between the browser and external service
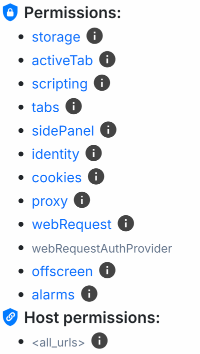
Individually, each of these access types may seem technical or harmless. But together, they define the actual operational boundary of what an extension can observe or interact with inside the browser.
This is why understanding browser extensions is critical in the context of modern trucking dispatch software ecosystems. The visible interface of a tool only represents its functionality - not its full technical reach.
The real capabilities of a browser extension are not defined by what you see in its interface, but by the level of access it has inside the browser environment.
Where Real Risk Appears in Logistics
When discussing browser-based tools and trucking dispatch software, it is easy to focus on features - automation, speed, integration, and convenience. But the real question for logistics companies is not what these tools can do, but what they can potentially observe or influence within operational workflows.
In a fully digital dispatch environment, even small layers of access can translate into meaningful business exposure. This is especially relevant in ecosystems that rely on dispatch automation and AI dispatch software, where tools are often embedded directly into high-frequency decision-making processes.
To understand the actual risk, it is useful to break it down into three practical categories.
Access to Accounts and Active Sessions
One of the most sensitive areas in modern logistics operations is authenticated access.
Dispatch teams constantly work inside logged-in environments - load boards, broker platforms, carrier portals, and financial systems. These sessions contain the operational “live state” of the business.
If a browser-based tool has access to session-level data, it may interact with authenticated environments in ways that are not always obvious to the user.
The risk here is not limited to technical access - it extends to operational continuity. Many dispatch software for trucking companies workflows depend on stable and trusted session environments. Any unintended interaction with these sessions can introduce account-level exposure across critical platforms such as load boards or broker systems.
Commercial and Operational Data
The second layer of risk relates to the actual business information being processed inside the browser.
Every day, dispatchers handle highly sensitive commercial data, including:
- Freight rates and pricing structures
- Load details and shipment characteristics
- Broker and carrier contact information
- Route and delivery parameters
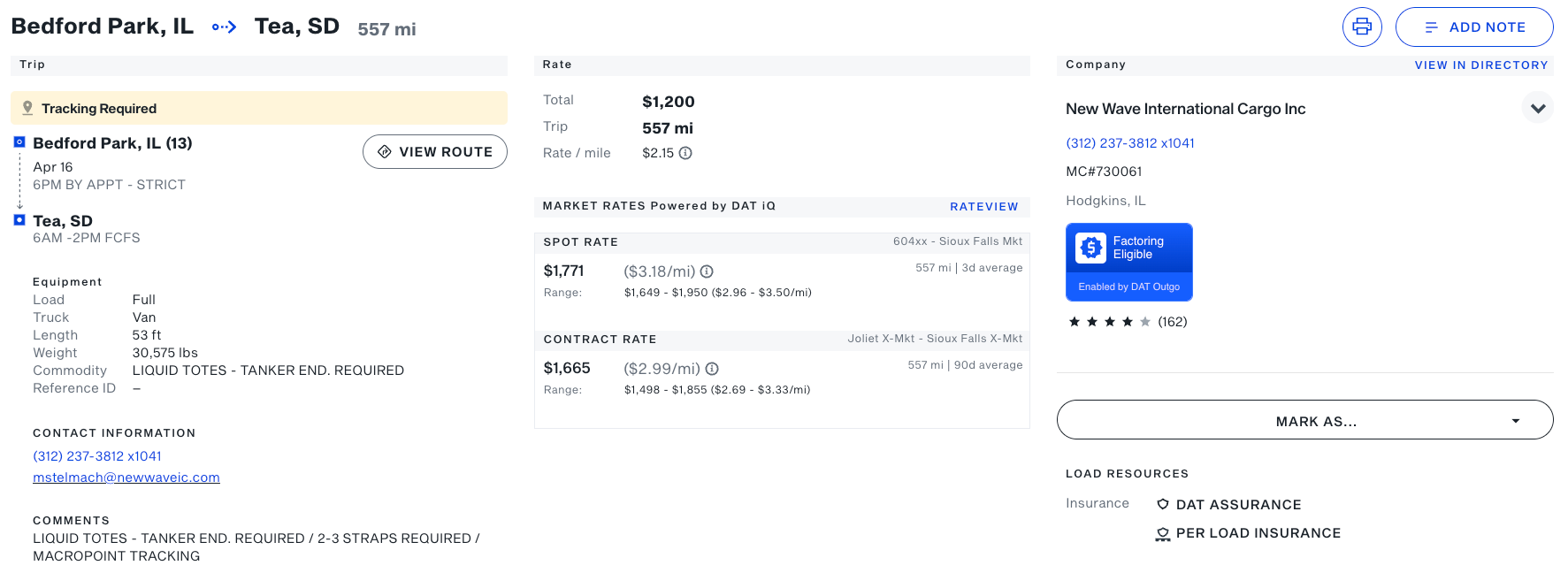
In environments powered by AI dispatch software, this data is constantly being processed, compared, and evaluated in real time. Even short-lived visibility into this information can represent meaningful business intelligence.
From a business perspective, this is not just “data on a screen” - it is the operational core of pricing decisions, margin control, and customer relationships.
Behavioral and Strategic Patterns
The third layer of risk is often the least visible, but one of the most important: behavioral data.
This includes patterns such as:
- How dispatchers search for loads
- Which loads are opened, ignored, or selected
- How pricing decisions are made over time
- How teams respond to market conditions
Individually, these actions may seem insignificant. But when observed over time, they can form a detailed picture of how a company operates - including decision-making logic, market strategy, and internal workflows.
In modern dispatch automation systems, these behavioral signals are increasingly valuable because they reflect not just what data is seen, but how that data is used.
Even seemingly harmless pieces of information - account access, load data, and user interactions - become significantly more powerful when combined.
Individually, they are data points.
Together, they form a complete operational map of a business.
LoadConnect Approach: Security as a Constraint, Not a Promise
At this point, the difference in approach becomes clear.
Most tools in the logistics space - including many products in trucking dispatch software and dispatch automation - are built around a trust-based model. They position security as something external to the system itself: policies, safeguards, compliance rules, and operational guidelines.
In simple terms, the message is usually: “We protect your data.”
This model depends on trust - trust in processes, trust in enforcement, and trust in how the system is operated behind the scenes.
LoadConnect takes a fundamentally different approach.
Instead of relying on assurances, LoadConnect is designed around a more strict and structural principle: “We are built in a way that there is simply nothing to steal.”
Security Built Into Architecture
In LoadConnect, security is not treated as a separate layer added on top of functionality. It is embedded directly into the system’s structure.
This means that protection is not dependent on policies or post-deployment controls. Instead, it is a direct consequence of how the system is designed and what it is technically capable of accessing in the first place.
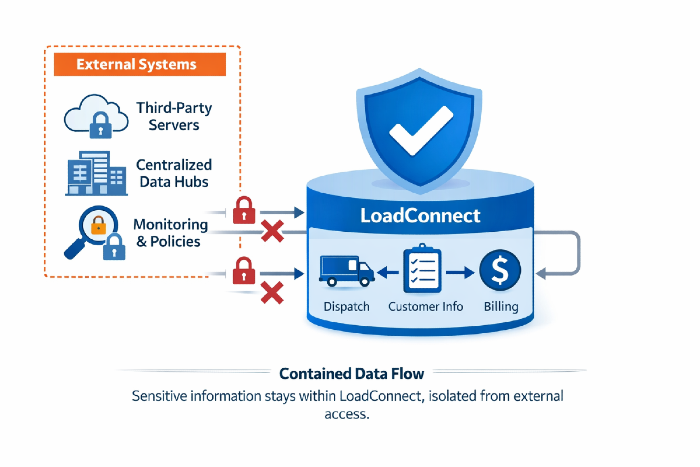
Unlike traditional AI dispatch software, where security is enforced through rules and monitoring, LoadConnect reduces exposure by removing entire categories of access from the system design itself.
No Reliance on Trust-Based Security Models
In most systems used in dispatch software for trucking companies, security depends on multiple external assumptions:
- That internal policies are followed correctly
- That access rules are enforced consistently
- That operational processes remain unchanged over time
- That sensitive data is handled only as intended
The limitation of this model is structural: security depends on behavior.
LoadConnect removes this dependency.
Instead of asking users or operators to trust the system, LoadConnect eliminates the conditions where misuse or unintended access could even occur.
A Different Definition of Safety
From a product perspective, this creates a fundamentally different security model.
- Security is not enforced after data exists
- Security is not monitored in real time
- Security is not dependent on human behavior or policy compliance
Instead, security is defined at the architectural level:
- What the system can access
- What the system can store
- What the system can transmit
Why This Shift Matters
In environments driven by AI dispatch software and browser-based automation, complexity often grows faster than visibility. As systems become more capable, their internal boundaries become harder to understand from the outside.
LoadConnect reverses this direction.
Instead of expanding capabilities and then controlling them through policies, it defines strict capability boundaries from the start.
Core Idea
Security is not something that is added to the system later. In LoadConnect, security is a direct result of system limitations.
It does not depend on trust, rules, or enforcement -it depends on what the system is fundamentally capable of doing.
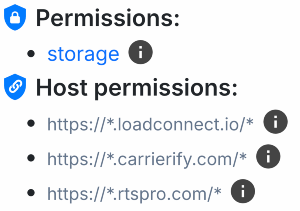
What Exactly Is Limited in LoadConnect (in Simple Terms)
To understand LoadConnect’s approach to security, it helps to clearly define what the system does not do. Unlike many tools in the trucking dispatch software ecosystem, LoadConnect is intentionally built with strict boundaries that remove entire categories of access from its design.
This is not about hiding features or restricting them through settings. It is about not including them in the system at all.
LoadConnect does NOT have access to:
• Passwords or browser cookies
LoadConnect does not store passwords or session data on its servers. Any session information stays on the user’s device and is not transferred or accumulated centrally.
• Browser network traffic
It does not monitor, intercept, or analyze what is being sent or received between your browser and external platforms.
• Data from other websites outside user actions
LoadConnect does not access information from platforms the user is not actively working with at that moment. There is no cross-site visibility or background extraction.
• Hidden background data collection
There is no silent tracking, logging, or continuous data gathering happening in the background while the browser is open.
• Hidden or invisible processes outside the browser window
All activity is tied directly to what the user is actively doing. There are no hidden execution layers running outside the visible browser context.
If a feature is not required for the product to function, it is not partially disabled or restricted - it is simply not part of the system.
In LoadConnect, the safest capability is the one that does not exist at all.
The Core Principle: “Minimum Necessary Access”
At the heart of LoadConnect is a simple but strict philosophy: the system should only have access to what is absolutely required for it to function - nothing more.
This approach is especially important in environments like trucking dispatch software, where tools often run continuously in the background, collecting data, syncing information, or operating beyond the user’s immediate actions.
LoadConnect is designed differently.
The system only works when the user is actively using it
LoadConnect does not run as an always-on background system. It is not observing, analyzing, or collecting information while the browser is open in the background.
Instead, it operates only during explicit user interaction - when the user is actively performing an action inside the system.
No background observation
There is no silent monitoring of user behavior, browsing activity, or external platforms. LoadConnect does not “watch” what happens in the browser outside of direct, intentional use.
This is a key difference compared to many AI dispatch software solutions, where background processes are often used to enable automation, analytics, or optimization features.
No hidden channels
LoadConnect does not create secondary or invisible data paths in the system. There are no hidden flows where information is collected outside of the user’s awareness or control.
No expanded permissions for future use
Some systems request broader access than they currently need, with the idea that it may be useful later for future features.
LoadConnect does not follow this approach.
It does not request or reserve permissions “just in case.” Every capability is tied to an immediate, clearly defined function.
LoadConnect is built on a straightforward rule: It only works when the user is actively using it - and only for that moment of interaction.
Nothing runs in the background. Nothing observes silently. Nothing exists beyond the user’s direct action.
LoadConnect Security Model Compared to Typical Browser Extension Architectures (Logistics Tools)
LoadConnect is not just another browser extension with stricter rules.
It is a fundamentally different architecture where security is not enforced externally - it is defined by system limitations.
Instead of restricting access to data, LoadConnect eliminates the possibility of collecting it in the first place.
What Happens in the Worst-Case Scenario
When evaluating any system used in trucking dispatch software or dispatch automation, the most important question is not how it works under normal conditions - but what happens if something goes wrong.
In other words: what is the real impact of a worst-case scenario?
This is where LoadConnect’s architecture becomes fundamentally different from most AI dispatch software solutions.
Even in a hypothetical compromise scenario
Let’s assume a situation where the system is somehow partially compromised or externally interfered with.
Even in that extreme case, LoadConnect is designed so that there is no meaningful centralized asset that could be extracted or misused at scale.
No password database exists
LoadConnect does not store user passwords in any centralized system. There is no single location where authentication data is collected, aggregated, or kept for later access.
This removes one of the most common high-impact targets in traditional systems.
No centralized accounts or shared identity layer
Unlike many platforms in the dispatch software for trucking companies ecosystem, LoadConnect does not rely on a shared account infrastructure that could be targeted at scale.
There is no unified identity system that connects users through a central authentication hub.
Each session exists independently, without a global account layer that can be compromised.
No accumulated user data repository
LoadConnect does not store or aggregate sensitive operational data in a centralized system.
While limited product analytics (e.g. user interaction events) may be collected, they are strictly separated from business data and do not include loads, pricing, or dispatch operations.
Why this changes the risk model
In most systems, especially in AI dispatch software environments, security risk scales with centralization. A single breach can potentially expose data across many users.
LoadConnect removes this structure entirely. There is nothing centralized to scale an attack against, and no shared layer where data accumulates over time.
This is not about reducing risk through monitoring or defense layers. It is about removing the conditions that make large-scale impact possible in the first place.
There is no single point of catastrophic failure - because there is no centralized system that concentrates that risk.
User Isolation: Each Customer Works in Their Own Separate Environment
One of the core principles behind LoadConnect is strict user isolation. In many modern trucking dispatch software platforms and AI dispatch software systems, user data is processed within shared infrastructure layers. Even when accounts are separated logically, the underlying systems may still rely on shared data processing, analytics, or optimization layers.
LoadConnect is built differently.
Data does not cross between users
Each LoadConnect user operates inside a fully isolated environment. There is no sharing of operational data, behavior, or activity between accounts.
This means one company’s dispatch activity, workflows, and decisions remain completely independent from another.
No shared analytics layer
Many systems in the dispatch automation ecosystem rely on aggregated data to improve performance, optimize recommendations, or refine system behavior.
LoadConnect does not use a shared analytics model across users. There is no centralized dataset where user activity is combined, compared, or analyzed together.
This ensures that each business operates based only on its own environment - not influenced by external user behavior.
No training or learning on customer data
In some AI dispatch software platforms, user data may be used to improve algorithms, train models, or optimize system-wide performance.
LoadConnect does not operate on this principle.
User activity is not used to train shared models or improve other customers’ experiences. Each user environment remains independent.
User isolation is not just a technical detail - it is a structural decision. Your business does not become part of a shared data system, and your activity is never used outside your own environment.
Why This Matters Specifically for Logistics
Security in logistics is not an abstract IT concern. It directly affects how companies operate, compete, and maintain profitability on a daily basis.
Unlike many other industries, logistics runs on highly time-sensitive and commercially sensitive information. This is especially true in environments powered by trucking dispatch software, where decisions are made in real time and often under pressure.
Logistics data is inherently sensitive
Every dispatch operation involves data that has immediate financial and operational impact:
- Freight rates and margins
- Route planning and delivery constraints
- Contracts and broker agreements
- Carrier relationships and availability
In systems built around dispatch automation and AI dispatch software, this information is constantly processed, compared, and acted upon - often within a single workflow session.
A data leak is not just a technical issue
In many industries, data exposure is primarily a security or compliance problem.
In logistics, the impact is more direct.
A leak or unintended exposure of operational data can immediately affect:
- Pricing strategy and competitive positioning
- Customer relationships and trust with brokers or carriers
- Profit margins on specific loads or lanes
- Long-term contract stability
Even small pieces of information - like rate structures or routing behavior - can have real financial consequences when exposed in the wrong context.
Operational stability depends on data control
Because logistics is highly competitive and fast-moving, companies rely on predictable control over their operational data.
This means security is not only about preventing breaches - it is about ensuring that core business information remains:
- contained
- predictable
- and strictly controlled within its intended environment
In platforms like dispatch software for trucking companies, even small weaknesses in data handling can translate into operational instability.
Key takeaway
In logistics, security is not just a technical feature of software. It is a foundational requirement for stable business operations. If your data is exposed, your operations are exposed.
Final Thought: A New Model of Trust in Software
Across the logistics technology landscape - from trucking dispatch software to modern dispatch automation platforms - most products still rely on a traditional idea of trust.
The message is usually simple: “Trust us to handle your data responsibly.”
This is a model built on promises, policies, and operational discipline. It assumes that everything works correctly because it is intended to work correctly.
But as systems become more complex - especially with the rise of AI dispatch software and AI browser extension tools embedded directly into workflows - trust alone becomes harder to evaluate in practice.
From trust-based systems to constraint-based systems
There is a fundamental shift happening in how software security is designed.
The old approach: “We define rules and expect them to be followed.”
The new approach: “We design systems where breaking the rules is not structurally possible.”
In a trust-based model, security depends on behavior - users, systems, or policies working exactly as intended.
In a constraint-based model, security is defined before the system even runs - by limiting what the system is capable of doing in the first place.
What this means in practice
In traditional systems, security is something that must be continuously maintained:
- permissions must be managed
- policies must be enforced
- behavior must be monitored
- edge cases must be controlled
In a constraint-based system like LoadConnect, the question is simpler: “Is this even possible within the system’s design?”
If the answer is no, then no additional enforcement is required.
LoadConnect does not ask you to trust it - it is architecturally built so that the scenarios where trust could be broken do not exist.
Explore LoadConnect and see how a constraint-based architecture changes security in logistics.